Cybersecurity
1. Introduction.
MonoM is strongly committed to information security. In order to provide businesses and their users with a secure experience, its solution is built applying universally accepted industry principles.
Every new development carried out by the MonoM team applies principles such as privacy by design and minimization. A sizable portion of the company’s quality team effort is spent on security testing. In addition, the solution is built on a public cloud, GCP, which has the highest cybersecurity standards.
a. Data Encryption
Cloud apps are not protected by traditional methods such as firewalls, so they must rely on data encryption and key management. Many customers are not comfortable leaving this vital task to data vendors and prefer to manage their own keys through a local hardware facility. In MonoM, Data “in motion” is protected using Transport Data Encryption (TDE). Other data transfer via HTTP (Hypertext Transfer Protocol) or FTP (File Transfer Protocol) are not used in MonoM, instead we use methods such as Transport Layer Security (TLS) and its secure protocols (HTTPS, SFTP…)
b. Adequacy of controls to the level of risk
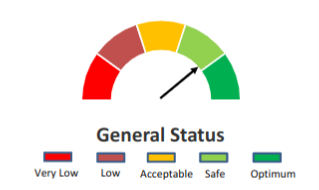
Security controls can be defined based on the SaaS (software as a service) provider’s acceptable levels of risk. Any control over data access, processing and monitoring will inevitably impact system performance, and a balance must be struck. The MonoM team has succeeded in finding a solution that offers optimal performance and security. To this end, use is made of secure protocols and tools offered by cloud providers to assist in this purpose.
c. Effective Identity and Access Management Controls
Identity and Access Management (IAM) tools prove that users are who they are supposed to be. There is a critical requirement for SaaS users to be able to integrate with IAM tools. Enterprise users do not want a different password whenever they access another part of an enterprise-wide platform. Sophisticated access control determining who accessed what and when is an essential element in any IAM system. In MonoM, we use Firebase to meet this requirement.
d. Logging and Monitoring
It is vital to log all access attempts into the SaaS system, both failed and successful. The same is true of any data amendments. Such activity is essential in mitigating data breaches and for establishing future security plan arrangements. In MonoM, we use Firebase records that allow us to log and alert about access attempts.
e. Secure Vaults
MonoM uses kubernetes as PaaS, and one of these features is kubernetes secret that allows to store and crypt keys in a secure way.
f. Security-first Software Development Life Cycle
As already mentioned, for the MonoM team, security starts from the design stage, translating security best practices throughout the development cycle, and ending with security testing by the quality team. Additionally, the solution has been audited by a third-party company expert in auditing and cybersecurity.
g. Data Management
As far as information security is concerned, the platform implements the fundamental principles of integrity, availability, and confidentiality.
- Integrity
MonoM ensures that the information is correct and has not been modified, and that the data remain exactly as they were when generated, without any manipulation or alteration from third parties. - Availability
MonoM ensures that access to the information is made via the appropriate channels in accordance with the proper processes. - Confidentialy
MonoM ensures that the information cannot be disclosed to unauthorised persons or systems.
3. Google Cloud Security.
Google Cloud undergoes independent security, privacy and compliance reviews to help customers meet regulatory and policy objectives. Detailed compliance information on all assurances of compliance with ISO/IEC 27001, 27017, 27018 and 27701; SOC 1, 2 and 3; PCI DSS, and VPAT (WCAG, US section 508, EN 301 549); as well as FedRAMP certifications; HIPAA; GDPR; and CCPA, among other regulations, can be found in the Google Resource Center.

Ref: https://cloud.google.com/security/compliance/offerings
GDPR
The General Data Protection Regulation (GDPR) is a privacy legislation that replaced the 95/46/EC Directive on Data Protection of 24 October 1995 on May 25, 2018. GDPR lays out specific requirements for businesses and organizations who are established in Europe or who serve users in Europe. It:
- Regulates how businesses can collect, use, and store personal data
- Builds upon current documentation and reporting requirements to increase accountability
- Authorizes fines on businesses who fail to meet its requirements
Google Cloud champions initiatives that prioritize and improve the security and privacy of customer personal data, and allows us to their customers, to feel confident using our services in light of GDPR requirements. Google Cloud will support GDPR compliance efforts by:
- Committing contracts to comply with the GDPR in relation to processing of customer personal data in all Google Cloud and Google Workspace services
- Offering additional security features that may help to better protect the personal data that is most sensitive
- Giving the documentation and resources to assist in privacy assessment
- Continuing to evolve our capabilities as the regulatory landscape changes
At MonoM, we use GCP products and services to offer our clients a security framework that allows them to operate with maximum guarantees.
Some of the products we use are: Bigquery for data storage, which allows us to apply data access policies, always verify its integrity and availability, pub/sub for sending messages securely and ensuring delivery, storage as a distributed file system or the managed PaaS kubernetes. In addition, the entire infrastructure is managed by Google, which is responsible for patches and security updates on machines and products, allowing the MonoM team to focus its efforts on providing greater added value to its customers. User management is centralized in Firebase.
Finally, we make use of security services provided by Google that actively monitor the health of the DMZ.
4. Third-party Audit
S21SEC is considered one of the leading European cybersecurity companies.
Monom has submitted its platform to a voluntary audit, obtaining the secure application qualification by S21SEC.